You’ve invested heavily in state-of-the-art access control, robust cybersecurity protocols, and a highly trained security team. Your facility is a fortress. But what about your suppliers? In today’s interconnected business landscape, your cybersecurity and physical security are only as strong as the weakest link in your supply chain. A vulnerability in a vendor’s system can become a direct threat to your operations, data, and reputation.
The Invisible Backdoor to Your Business
Modern businesses are deeply integrated with third-party partners. These suppliers often have access to your networks, intellectual property, shipment schedules, and even your building management systems. A hacker targeting a smaller, less-secure supplier can find a backdoor into your own organization. This isn’t a theoretical risk; major breaches have started through vulnerabilities in HVAC vendors, logistics partners, and software providers. When you grant a supplier access, you are implicitly trusting their security posture. If that trust is misplaced, the consequences can be catastrophic.

Beyond Data: The Physical Threat
The risk isn’t confined to data theft. Consider a logistics provider with weak access controls on their tracking system. A bad actor could manipulate shipment information, reroute deliveries, or even orchestrate the theft of high-value goods in transit. An attacker could exploit a supplier’s weak password policies to gain access to your building’s HVAC or energy management systems, threatening operational continuity. The blurring line between digital and physical security means a software flaw at a partner’s office can lead to a very tangible, physical loss at your facility.
3 Steps to Build a Resilient Supply Chain
Ignoring this threat is a gamble you can’t afford to take. Proactive management is key. Here’s how to start:
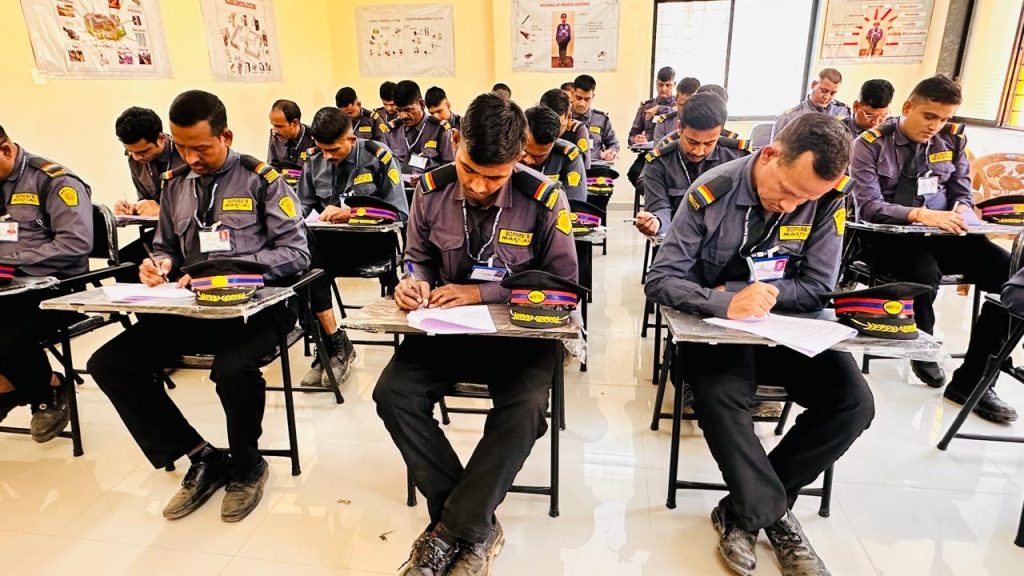
- Vet and Assess: Don’t assume compliance. Make robust security practices a mandatory part of your vendor onboarding process. Require partners to complete detailed security questionnaires and, for critical suppliers, commission independent audits to verify their protocols. Ask about their access control measures, employee training, and incident response plans.
- Limit and Monitor Access: Adhere to the principle of least privilege. Grant suppliers only the minimum level of access absolutely necessary to perform their job. Segment your networks to ensure vendor access points are isolated from your most critical systems. Continuously monitor all third-party access for unusual activity.
- Contract for Security: Your legal agreements should explicitly outline security requirements, reporting obligations, and liability. Suppliers must be contractually obligated to notify you immediately of any breach that could impact your data or operations. This ensures transparency and enables you to respond swiftly to mitigate damage.
Your Security is Your Responsibility
Ultimately, you cannot outsource your risk. A breach originating from a supplier will still bear your company’s name in the headlines. By taking a rigorous, proactive approach to supply chain security, you move from implicit trust to verified confidence. You protect not just your assets, but your brand’s integrity and your customers’ trust.
Are you confident in your suppliers’ security? Eyeonix’s risk assessment services include comprehensive vendor security evaluations. Contact us today for a confidential consultation to fortify your entire supply chain.
